Gleiss Lutz regularly assists companies with data breaches from start (immediate response) to finish (remedial measures, root cause analysis) and advises on complying with legal cybersecurity requirements. This includes coordinating any immediate action required by law (especially in the event of cyberattacks), negotiating with attackers, communicating with regulators and law enforcement, liaising with technical service providers and defending against claims for damages. We serve as Global Coordinating Counsel for our clients to address cross-border implications with a network of trusted partners. We also help clients review and upgrade their cybersecurity measures before – or after – an incident arises.
Cybersecurity – Integrated advice on the full spectrum of risks
As businesses increasingly integrate digital technologies, the imperative for robust cybersecurity grows. Companies encounter a myriad of practical and legal complexities in safeguarding against cyber threats. Our firm, with its team of multidisciplinary experts, guides businesses through these intricate challenges.
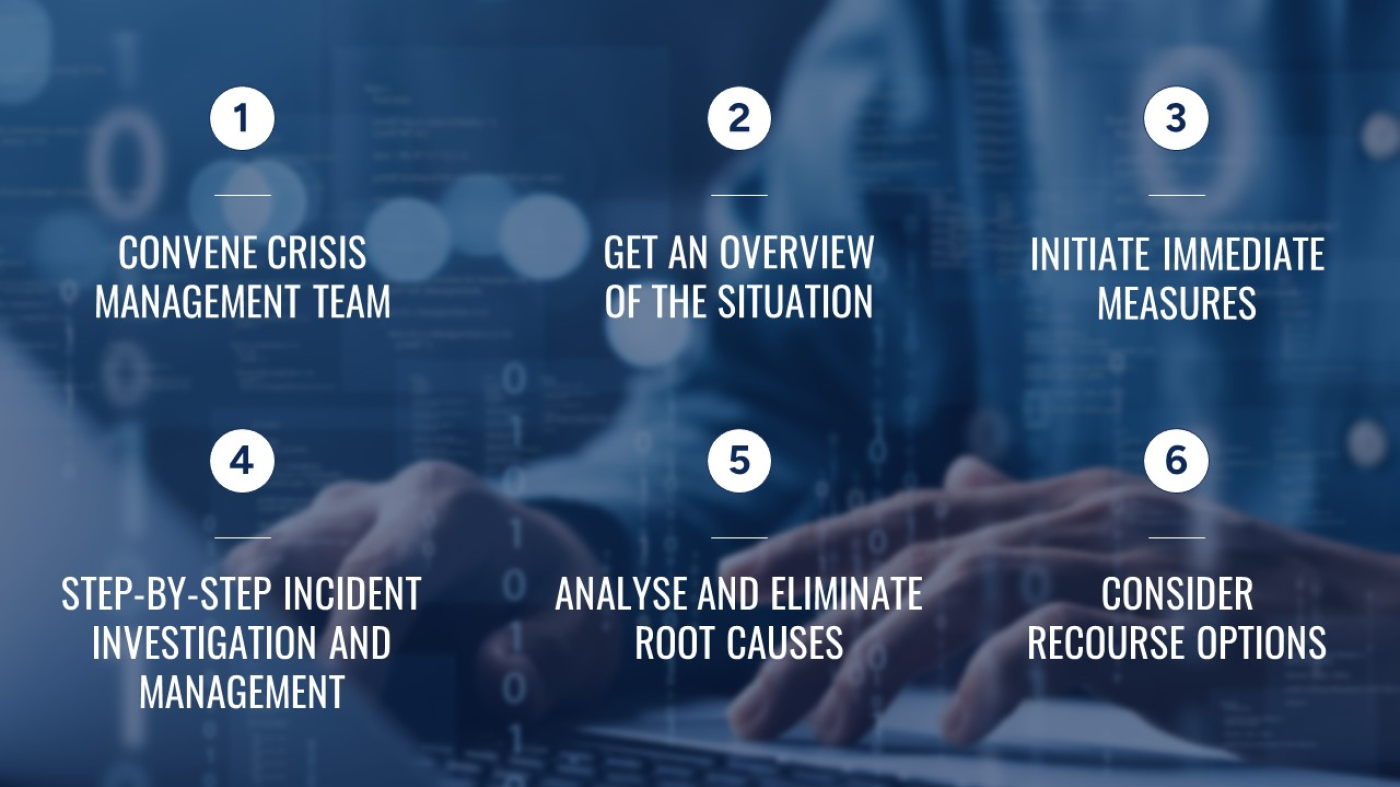
Responding to Cybersecurity Incidents – Managing data breaches
Has there been a breach in your company's data security?
- What are the necessary actions?
- What sequence should they follow?
Consider this response strategy as your initial guide.
Cybersecurity Readiness
The threat landscape itself and the associated legal issues make it very challenging for companies to properly plan for cybersecurity incidents. Is your company prepared? Find out with our cybersecurity check.